Have a Question?
TPM on the Vault
Overview
The Trusted Platform Module (TPM) is a dedicated, secure microcontroller used for cryptographic operations. A TPM is used to generate, store, and manage cryptographic keys. TPM is a standard defined by ISO/IEC 11889.TPM technology is becoming more popular as a mechanism to guarantee device integrity. As an example, Windows 11 requires a TPM 2.0 in order to install the OS. A key feature of TPM is that it can be used to "measure" the boot process as it proceeds through various stages. Each stage is checked against key(s) signed by a known authority. This must be implemented in the BIOS, it does not occur simply by installing the module in the unit. Protectli currently has not implemented this feature, plans to implement Secure Boot in a future release of BIOS.
TPM Hardware
The Protectli TPM-01 is a small circuit board with a connector that uses the Infineon SLB 9660TT upgraded to TPM 2.0. The product page for TPM-01 can be found at this link. The Protectli TPM-01 is compatible with the Vault Pro VP2410 and VP4600 series of products. The Protectli TPM-02 is compatible with the Vault Pro VP2420 and VP6600 Series and can be found at this link.
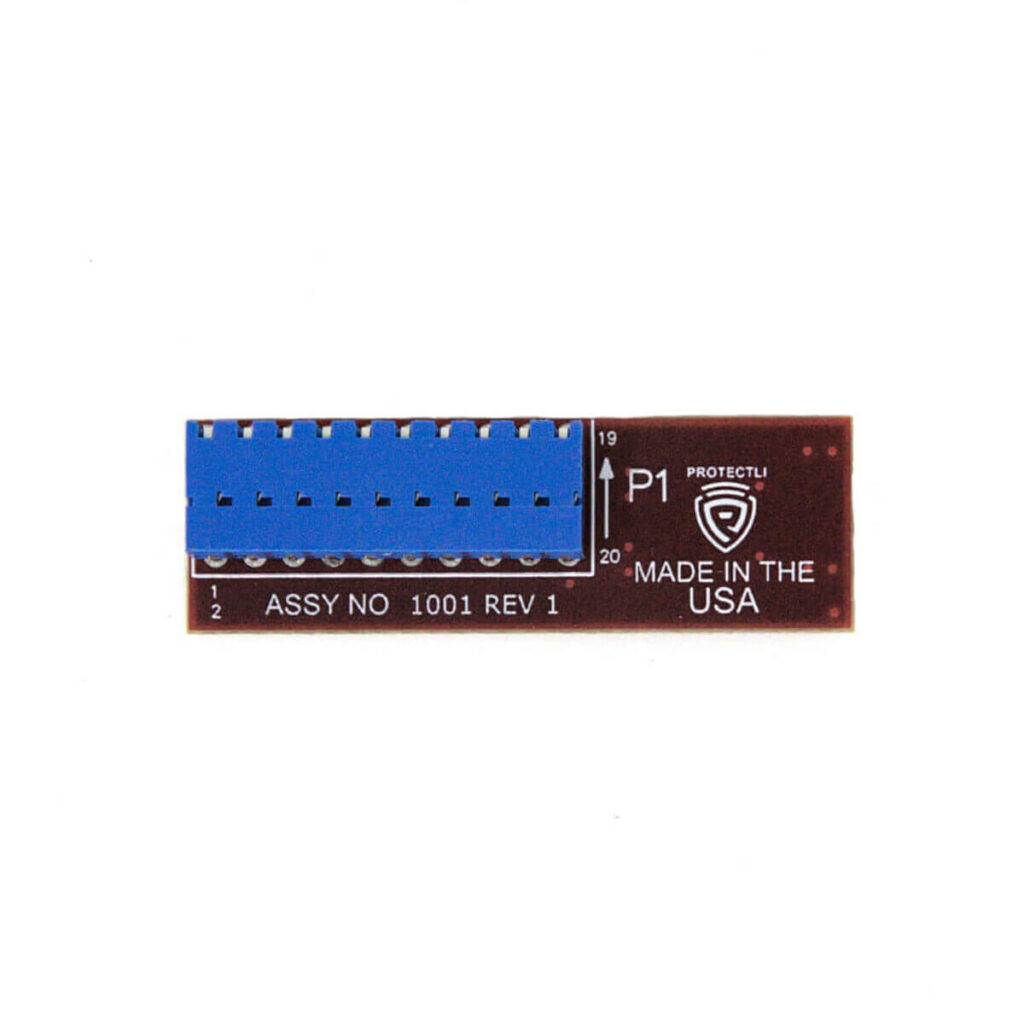
TPM-01
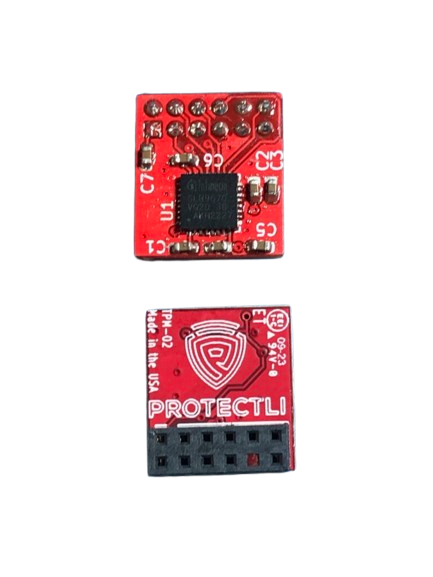
TPM-02
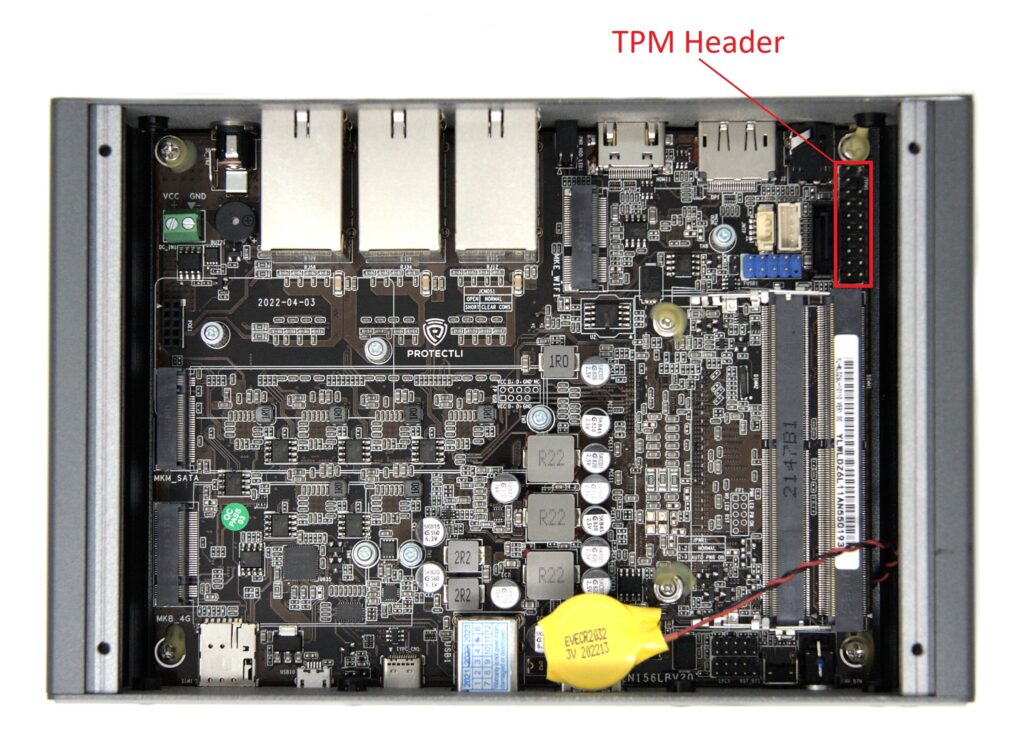
The TPM-01 has a keyed pin on the connector, so pin 4 of the TPM header on the VP2410 may need to be clipped in order to insert the module onto the board. The VP4600 series already has the pin removed, so you do not need to clip anything. When the TPM-01 is ordered with a VP series Vault, it comes inserted on the board. If the TPM-01 is ordered separately, pin4 on the VP2410 it may need to be clipped. In order to clip the pin with a standard dykes, the board must be removed from the chassis.
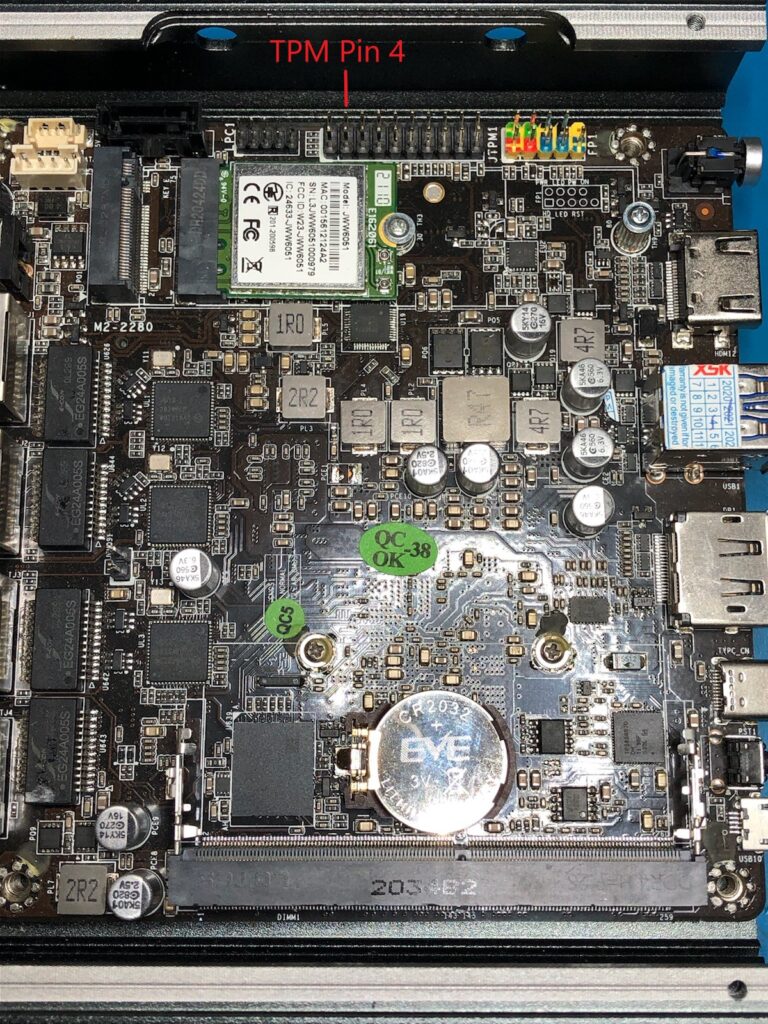
VP2410 TPM Header
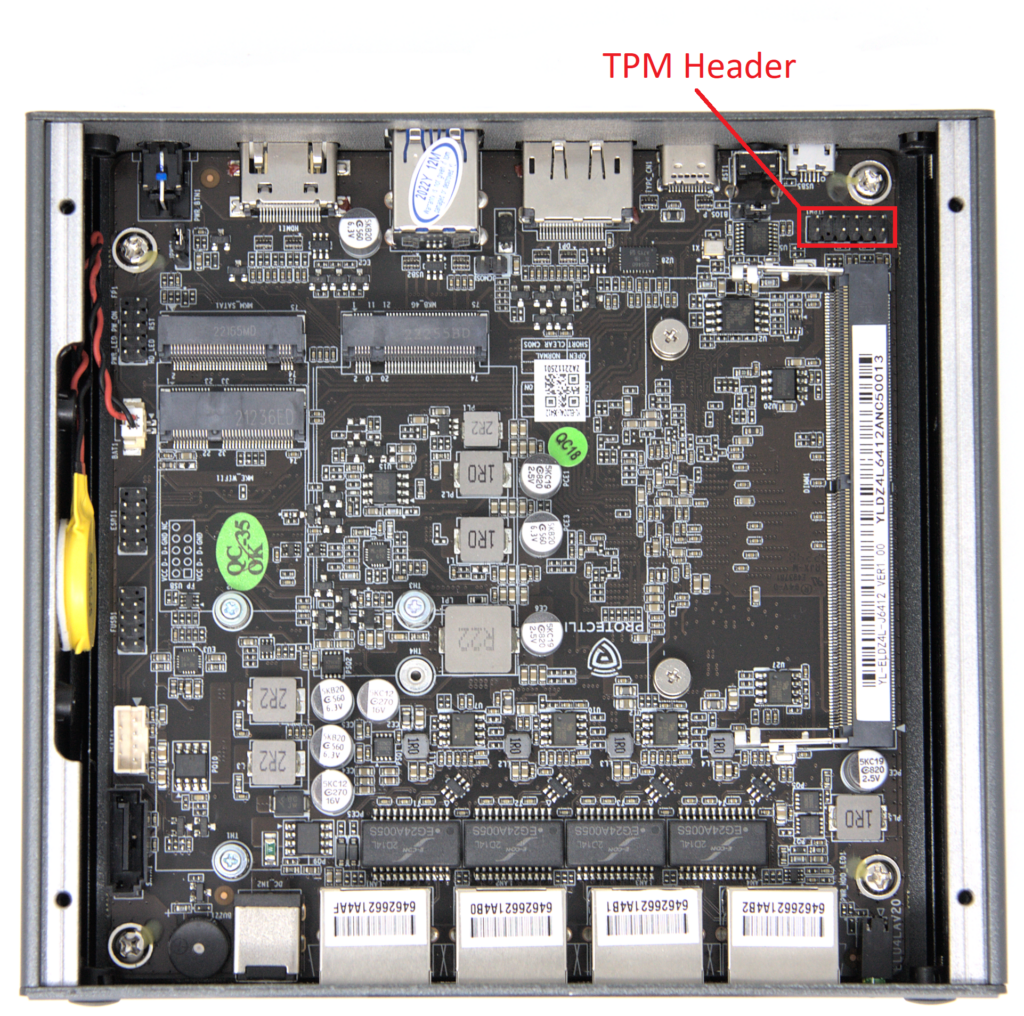
VP2420 TPM Header
VP4600 TPM Header
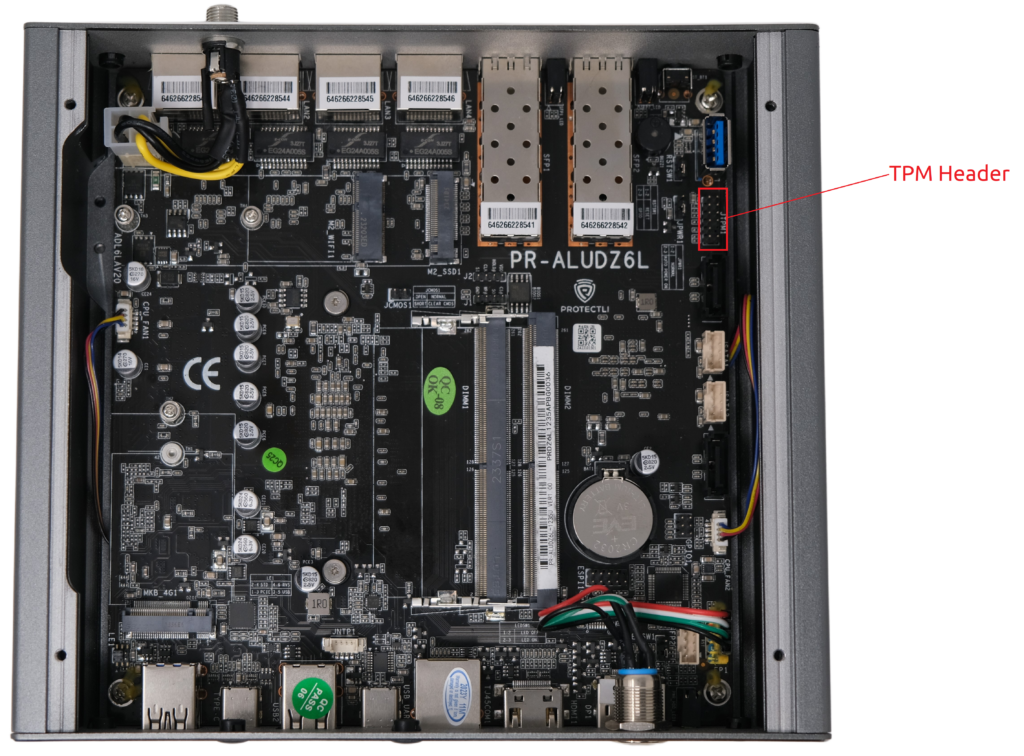
VP6600 TPM Header
BIOS
VP2410 AMI BIOS
In order to use TPM with AMI BIOS, it must be enabled in the BIOS. When booting, press the DEL key to get to the BIOS and enable the following settings: Advanced->Trusted Computing->Security Device Sup : [Enable] Advanced->Trusted Computing->TPM Device : [Enable]
VP2410 coreboot
The TPM will be enabled by default with coreboot.
VP2420 AMI BIOS
On a VP2420 with AMI BIOS, the TPM is typically automatically detected. To verify, press the DEL key during boot to get into BIOS settings. Navigate to Advanced->Trusted Computing. Verify that "TPM 2.0 Device Found" is displayed towards the top of the menu. Verify that "Security Device Support" is set to: [Enable]
VP2430/VP2440 AMI BIOS
On a VP2430 with AMI BIOS, a physical TPM can be configured in the BIOS menu. Hold the DEL key during boot to get into BIOS settings. Navigate to Advanced ->PTT Configuration ->and select [dTPM]. Make sure to save settings and reboot the Vault one time.
VP4600 AMI BIOS
The VP4600 comes with an on CPU TPM, referred to as "Firmware TPM" or Intel PTT. In order to use TPM with AMI BIOS, it must be enabled in the BIOS. When booting, press the DEL key to get to the BIOS and enable the following settings: Advanced->Trusted Computing->Security Device Sup : [Enable] In order to select the Protectli discrete TPM, enable the following: Advanced->Trusted Computing->TPM Device : [dTPM]
VP6600 AMI BIOS
The VP6600 comes with an on CPU TPM, referred to as "Firmware TPM" or Intel PTT. In order to use the dedicated Protectli TPM with AMI BIOS, it must be enabled in the BIOS. When booting, press the DEL key to get to the BIOS and enable the following settings: Advanced->PTT Configuration-> TPM Device Selection-> change to [dTPM]. Save settings and reboot. You can verify that the device is seen by going to Advanced-> Trusted Computing, you should see a note towards the top of the page saying "TPM 2.0 Device Found".
VP2420, VP2430, VP2440, and VP4600 coreboot
On the VP4600 series with coreboot, if a TPM is discovered by the system, it will automatically enable it. coreboot on the VP4600 includes Measured Boot. Measured Boot is a security feature that "measures", or checks, each stage of the boot process. Measured Boot also writes the hash digest from each stage into a TPM so that the OS can check/verify the value later. Further information can be found on this article.
OS
VP2410
Although Protectli has not implemented Secure Boot in BIOS, the TPM may be utilized if the OS supports it. As an example, Ubuntu 20.04 uses the TPM2 tools package and there is an article on Disk Encryption at: https://tpm2-software.github.io/2020/04/13/Disk-Encryption.html
VP2420, VP2430, VP2440 and VP4600 Series
coreboot on the VP2420 and VP4600 series has implemented Secure Boot, which may be utilized with the TPM if an OS supports it. Operating Systems such as Windows and Ubuntu support Secure Boot. These OSes have their public keys included in the coreboot image in order to verify the integrity of the OS. Further information regarding Secure Boot as well as other security features may be found on this article.
Summary
This has been a quick introduction to the Protectli TPM. As always, if you have any questions, feel free to contact support at support@protectli.com
