Have a Question?
pfSense® IPSec VPN Performance
*This article was originally created a few years ago, and used an older version of pfSense® and doesn't contain results of all Vault models. We are keeping this article up for now, but for a general updated version of expected VPN throughput can be found on this article instead.
pfSense IPSec VPN Performance
Overview
Depending on individual use cases, different hardware firewalls may be useful for different types of network applications and as such, Protectli offers different hardware with varying capabilities. Frequently, it is useful for a customer to know the performance characteristics of specific hardware before making a decision to purchase. This article aims to provide a baseline of IPSec performance for several different Vaults, as tested in a lab environment, so the customer can make an informed decision as to what products best suit their needs. We have also performed a separate set of tests with IPSec on OPNsense, results can be found here.
Basic Performance
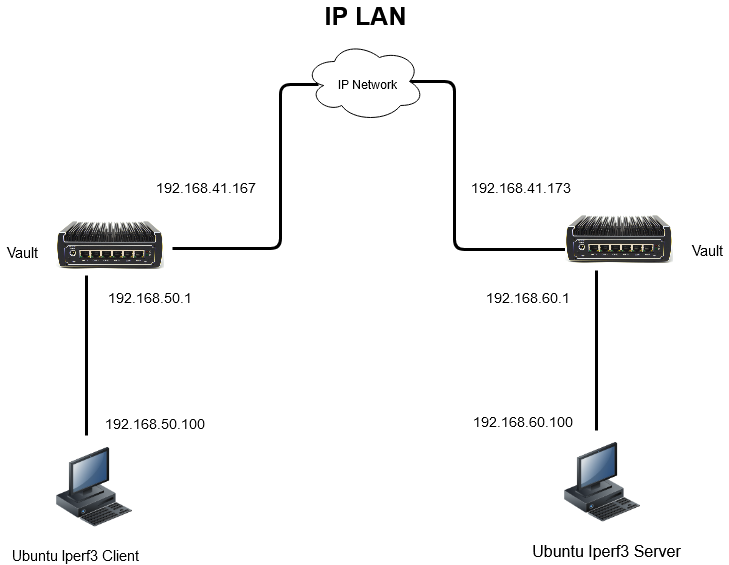
In a basic setup, The Vault is capable of routing packets at wire speed on all ports for all models. For a 1 Gbps ethernet interface, the actual data throughput is ~940 Mbps due to overhead in an IP packet. The test network consists of 2 computers running Ubuntu 20.04.1 version of Linux and 2 Vaults running pfSense® CE version 2.4.5_1. One of the Ubuntu computers is running iperf3 as a server, the other is running iperf3 as a client.
IPsec
IPsec is a set of protocols that is used to authenticate and encrypt/decrypt packets to provide secure transport of packets through the network. An IPsec "tunnel" encrypts the entire packet, not just the payload, and is commonly used to create Virtual Private Networks (VPN).
Configuring IPsec
When configuring IPsec tunnels (and other secure connections) multiple parameters must be configured. The set of parameters is known as a "cipher suite". The parameters consist of a Key Exchange method, an Encryption method and a Message Authentication method. The configuration must be identical at each end of the tunnel in order to make a connection. An operating system or IPsec implementation will typically support multiple ciphers for each of Key Exchange, Encryption, and Message Authentication that can be combined to form many different cipher suites. OpenSSL, which is an open source software library, provides a large number of ciphers. The list of ciphers supported can be displayed with the command "openssl ciphers –v". The cipher suite is described by combining the methods together into a single string. For example, the cipher DH-RSA-AES256-SHA256 indicates:
Diffie-Hellman (DH) Key Exchange using a Rivest, Shamir, Adelman key (RSA) with Advanced Encryption Standard 256 bit (AES256) encryption and Secure Hash Algorithm 256 bit (SHA256) message authentication.
There are various standards and recommendations that dictate the required cipher suite for different applications that is beyond the scope of this article.
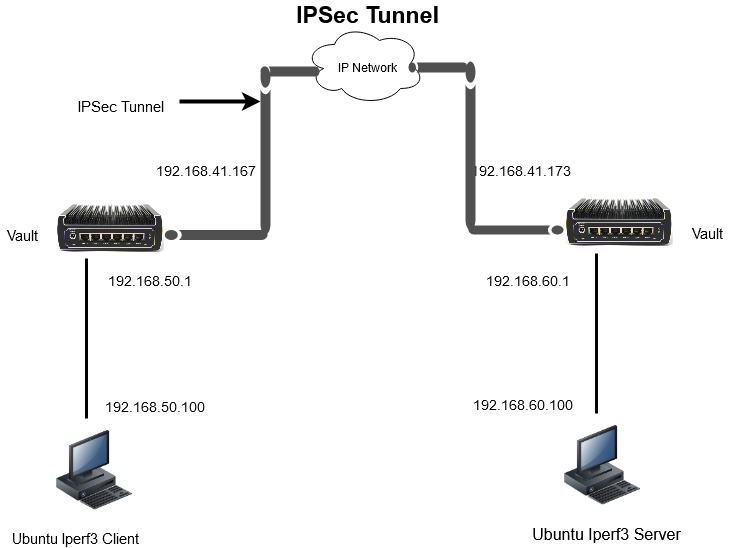
The diagram below shows an IPsec tunnel. The difference between the LAN example above and the IPsec tunnel is that the entire packet is encrypted "end-to-end" between the Vault/Firewalls and the data can travel through the network securely.
IPsec Performance
Adding an IPSec tunnel introduces "overhead" which is added when a packet enters a tunnel and stripped off when a packet leaves the tunnel. This process adds additional data to each packet, but is not part of the payload. Therefore, when running performance measurement tests, the indicated traffic throughput will be less than throughput achieved without an IPSec encrypted tunnel. In addition to the pure impact on the payload due to additional overhead, the device that adds the overhead must also encrypt the data. Similarly, the device at the other end of the tunnel receiving the packet must decrypt the data before sending it onward. Encryption and decryption of the packet requires significant processing power and affects the throughput of the devices. The latest versions of The Vault include Intel’s AES-NI hardware support which facilitates faster encryption/decryption with less impact on CPU performance. The performance varies depending on the parameters of the many different cipher suites. For example, a cipher suite that uses AES128 may perform better than AES256 due to easier encryption/decryption. It would be difficult if not impossible to test all possible cipher suites. For this purpose, a variety of different iterations have been tested, including ones that are not optimal in terms of performance, or commonplace. In order to test performance, pfSense® CE 2.4.5_1 was installed on the Vaults and IPsec tunnels were configured with the following initial cipher suite which provided the most optimal results found across all platforms:
Phase 1 settings:
- Diffie Hellman (DH) Key Exchange using Pre-Shared Key (PSK)
- AES128 bit encryption algorithm with AES-XCBC for the hash
Phase 2:
- AES128-GCM with 128 bit key length for the Algorithm
- No hash (Not indicated, AES-GCM provides authentication)
The configuration pages for VPN > IPSec > Tunels are shown below.
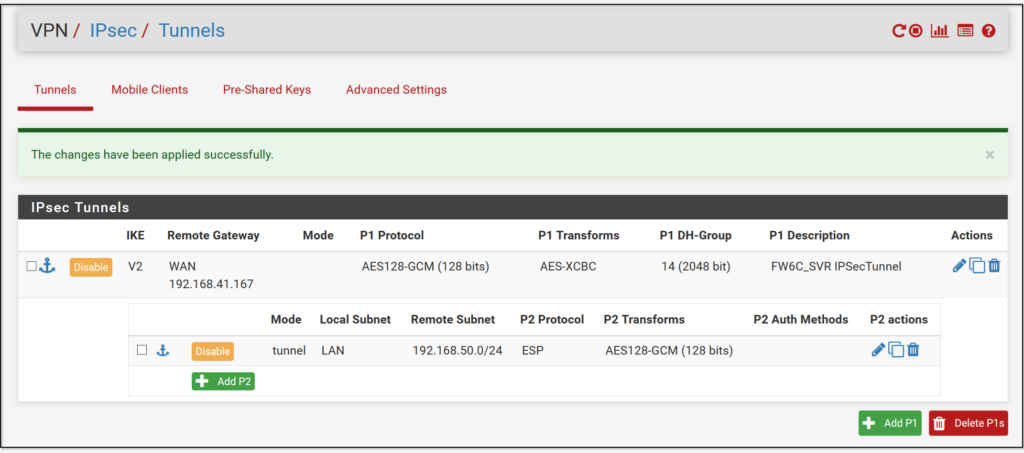
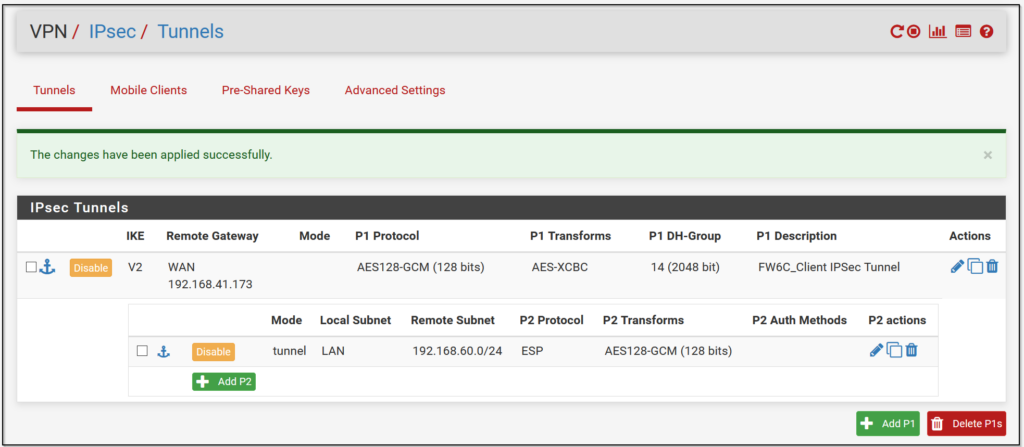
In this example, data from LAN network 192.168.50.0 is "tunneled" to LAN network 192.168.60.0 over the WAN interface. In the reverse direction, data from LAN network 192.168.60.0 is "tunneled" to LAN network 192.168.50.0 over the WAN interface. The max throughput as tested over the IPsec tunnel for a 1 Gbps Ethernet interface is ~880 Mbps, which is expected due to the overhead added by the IPsec configuration. The results of performance tests run on the Vaults that contain AES-NI hardware support are shown in the table below.
For more detailed information on the performance results, please click on the link: IPSec Performance Sheet
| Vault Model | Unencrypted (Mbps) "#iPerf3 -c -P4 -f m" | IPSec (pfSense) AES-128-GCM/AES-XCBC/ AES128-GCM "#iPerf3 -c -P4 -f m" | IPSec (OPNsense) 128 bit AES-GCM w/ 128 bit ICV/AES-XCBC/14 [2048 bits] DH/AES128gcm16/No Hash/14 [2048 bits] PFS "#iPerf3 -c -P4 f m" | OpenVPN (pfSense 2.7) AES-256-GCM/SHA256 (Mbps) "#iPerf3 -c -P4 -f m" | WireGuard (OPNsense)256-bit ChaCha20Poly1305 Avg (Mbps) "#iPerf3 -c -P4 -f m" | Wireguard (pfSense® 2.7.2) |
|---|---|---|---|---|---|---|
| FW2B | ~940 | ~520 | ~529 | ~114 | ~280 | |
| FW4B | ~940 | ~635 | ~747 | ~134 | ~290 | |
| FW4C | ~2300 | ~890 | ~807 | ~167 | ~315 | |
| FW6A | ~940 | ~875 | ~785 | ~491 | ~876 | |
| FW6Br2 | ~940 | ~875 | ~814 | ~850 | ~907 | |
| FW6C | ~940 | ~875 | ~821 | ~816 | ~907 | |
| FW6D | ~940 | ~875 | ~879 | ~894 | ~909 | |
| FW6E | ~940 | ~875 | ~879 | ~906 | ~909 | |
| VP2410 | ~940 | ~875 | ~809 | ~371 | ~733 | |
| VP2420 | ~2330 | ~1700 | ~1320 | ~450 | ~1200 | |
| VP2430 | ~2340 | ~2090 | ~2060 | ~905 | ~2260 | ~2200 |
| VP2440 | ~9380 | ~2620 | ~2500 | ~905 | ~4140 | ~3005 |
| VP4630 | ~2340 | ~2100 | ~1790 | ~1240 | ~2100 | |
| VP4650 | ~2340 | ~1900 | ~1910 | ~1290 | ~2160 | |
| VP4670 | ~2340 | ~1900 | ~2200 | ~1360 | ~2200 | |
| V1210/V1410 | ~2340 | ~1.15Gbps | ~800 | ~347 | ~1.1Gbps | ~1.2Gbps |
| V1610 | ~2340 | ~1.90Gbps | ~2.02Gbps | ~550Mbps | ~1.96Gbps | ~1.62Gbps |
Configuration Files for IPSec Performance Testing
Provided is the configuration files for both the IPSec server and IPSec client to be used for performance testing purposes. Please note that configuration changes will have to be made for the IPSec tunnel depending on the WAN IP address issued via DHCP.
| Config | IPSec Server | IPSec Client |
|---|---|---|
| FW6C Server to FW1 Client | FW6C_SVR to FW1 | FW1_Client |
| FW6C Server to FW2 Client | FW6C_SVR to FW2 | FW2_Client |
| FW6C Server to FW2B Client | FW6C_SVR to FW2B | FW2B_Client |
| FW6C Server to FW4A Client | FW6C_SVR to FW4A | FW4A_Client |
| FW6C Server to FW4B Client | FW6C_SVR to FW4B | FW4B_Client |
| FW6C Server to FW6A Client | FW6C_SVR to FW6A | FW6A_Client |
| FW6C Server to FW6B Client | FW6C_SVR to FW6B | FW6B_Client |
| FW6C Server to FW6C Client | FW6C_SVR to FW6C | FW6C_Client |
Conclusions on IPSec Performance
IPsec is a critical set of protocols used to provide secure communication through the Internet. There are many different cipher suites that can be used depending on the requirements of the user. The configuration used may impact the performance and therefore the throughput of the devices in the network. This tutorial is an aid to selecting the best Vault for your application. If you have any questions, feel free to reach out to us! You can submit a ticket here, find more information in our Knowledge Base, or visit the pages at IETF as reference.
